32+ Free Simple IT Risk Assessment Templates (PDF, Word)
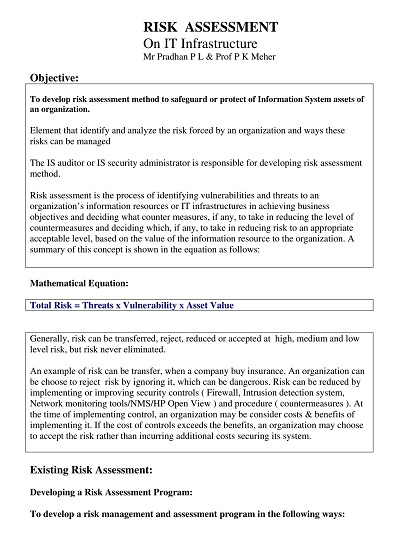
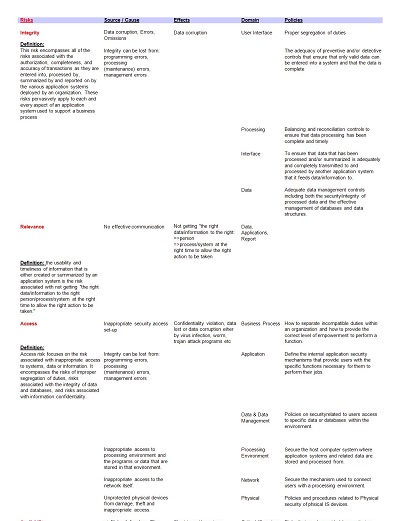
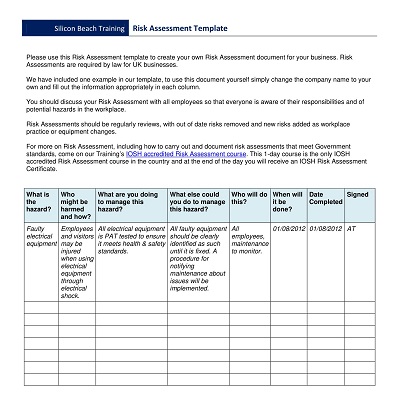
An IT Risk Assessment Template is a valuable tool for any organization looking to identify and mitigate potential risks to their technology infrastructure. This document outlines all potential risks to a company’s IT system and measures the likelihood of each occurrence and its potential impact on the organization. With this information, the company can prioritize the most critical risks and develop a plan to reduce or eliminate them.
Table of Contents
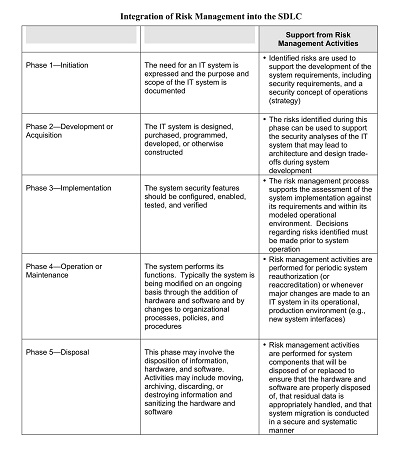
The Template helps ensure that risks to the IT system are identified as part of the business processes and assessed on an ongoing basis, which enables the organization to take corrective actions proactively. By conducting an IT risk assessment, the organization will not only be able to minimize risks but also seize opportunities and increase overall business performance.
Download Free Simple IT Risk Assessment Templates
Importance of IT Risk Assessment in Modern Organizations
As organizations become increasingly reliant on technology, the need for effective IT risk assessment becomes more and more critical. In today’s fast-paced business environment, companies must balance the constant demand for innovation with the necessity of ensuring that their data and systems are secure.
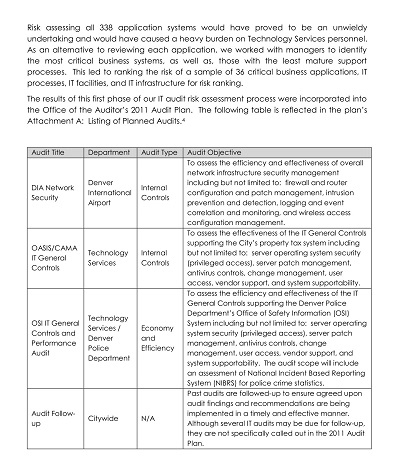
A comprehensive IT risk assessment can help identify potential vulnerabilities in a company’s IT infrastructure and develop strategies to mitigate those risks. By prioritizing IT risk assessment, modern organizations can stay ahead of cyber threats and protect their valuable data and assets. Whether you are a small start-up or a large corporation, taking the time to assess your IT risk is essential to the success of your organization.
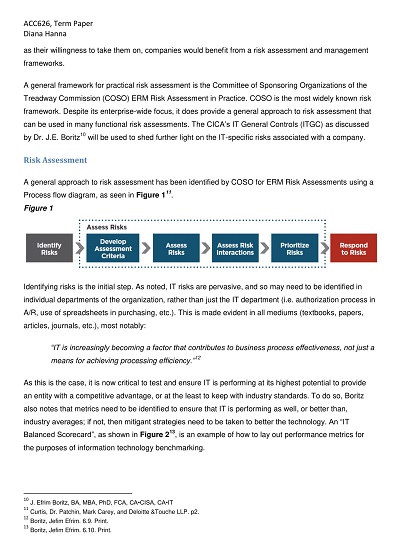
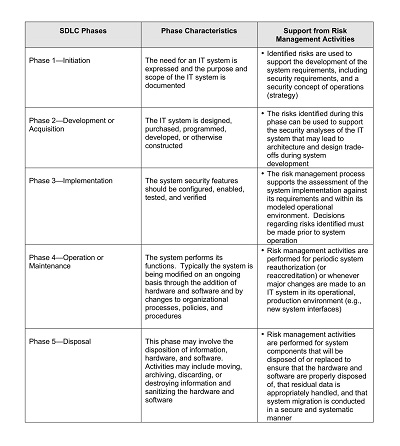
Key Components of an Effective IT Risk Assessment Framework
As technology continues to advance, businesses are increasingly relying on information technology (IT) systems to store and manage their data. However, with this, increased reliance comes a heightened risk of cyber-attacks and system breaches. It’s crucial for organizations to have an effective IT risk assessment framework in place to identify vulnerabilities in their systems and mitigate potential threats.
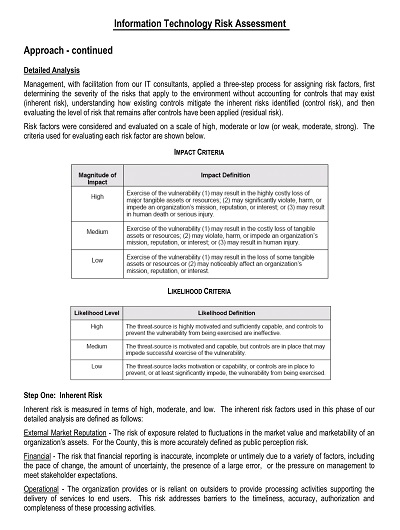
Key components of such a framework include proactive risk management strategies, regular risk assessments, data classification policies, incident response plans, and employee training programs. An effective IT risk assessment framework can save a business from significant financial loss, legal liabilities, and reputational damage. By prioritizing IT security, businesses can protect themselves and their clients from potential cyber threats.
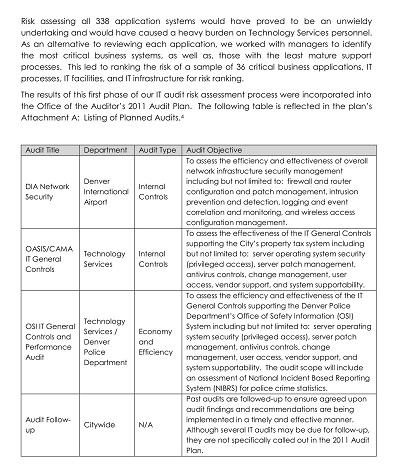
Step-by-Step Guide to Conducting an IT Risk Assessment
In today’s digitized world, organizations are heavily reliant on technology in their daily operations. However, with great power comes great responsibility, and as technology grows, so do the risks associated with it. To keep up with today’s ever-evolving cybersecurity landscape, organizations need to conduct a comprehensive IT risk assessment.
But where do you start? Don’t worry – we’ve got you covered with this step-by-step guide to conducting an IT risk assessment. From identifying your assets to creating a risk matrix, we’ll walk you through the entire process. With this guide at your fingertips, you can proactively manage IT-related risks and protect your organization’s critical data and infrastructure.
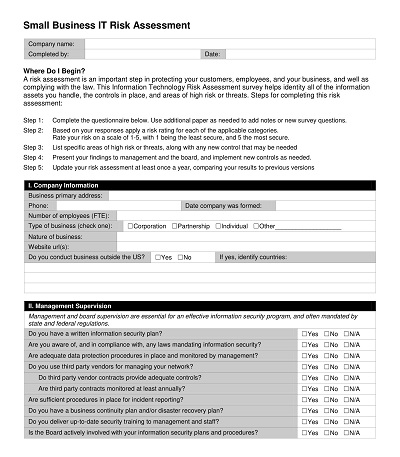
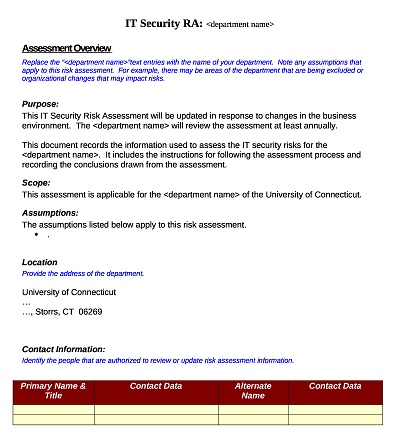
How to Create an IT Risk Assessment Template
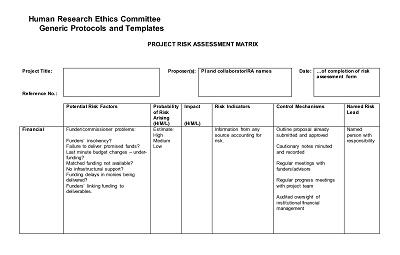
As businesses grow and rely more heavily on technology, IT Risk Assessment has become a crucial component of organizational risk management. A well-constructed IT risk assessment template will provide businesses with detailed risk analysis, which is crucial for managing and mitigating risks and security threats. However, creating an IT risk assessment template can be a daunting task, especially for those without an IT background.
- Identify All Assets: The first step in creating an IT risk assessment template is to identify all the assets in your business. You should know where everything is located, what it does, and who is responsible for it. Assets include hardware, software, data, personnel, and third-party vendors. By identifying all the assets in your business, you will be able to assess the risk associated with each asset and prioritize them for your risk management strategy.
- Identify Potential Threats: The second step in creating an IT risk assessment template is to identify potential threats. It includes understanding who can cause harm to your assets. Threats can come from an array of sources, including employees, ex-employees, hackers, natural disasters, or system glitches. It is vital to identify the likelihood of each threat and the impact they will have on your business if they occur.
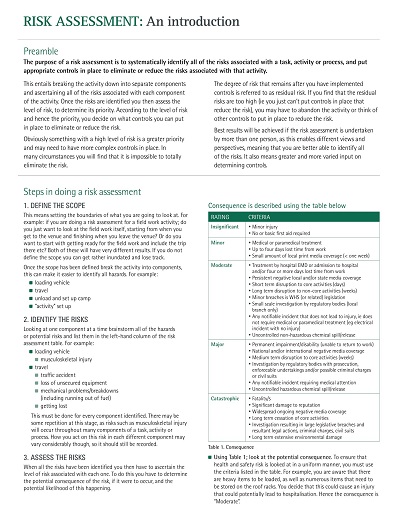
- Estimation of Risks: Once you have identified assets and potential threats, the next step in creating an IT risk assessment template is estimating the risks. It involves evaluating the probability of a threat causing harm to an asset and the severity of the damage it could cause. Risk estimation is one of the essential steps in creating an IT risk assessment template as it helps prioritize the risks that need to be addressed urgently.
- Creating a Mitigation Plan: The fourth step in creating an IT risk assessment plan is creating a mitigation plan. It involves developing a plan that contains measures to reduce the risk of any potential damage or loss to your assets. The mitigation plan should be based on the risks identified and include employee access and security protocol, disaster recovery plans, and cybersecurity measures.
- Regular Review: The final step in creating an IT Risk Assessment Template is regularly reviewing the plan. IT risk assessments should never be a set-it-and-forget-it activity. Regular reviews will help identify any new risks that may emerge. It will also help keep your security strategy up-to-date with the changing risk landscape.